Feeling Watched? How Websites Track You with Fingerprinting
September 25, 2023 • 0 minute read •
Every time you browse the web, you're being watched. Most of us are aware of cookies; the method websites use to track and tailor ads to us. But cookies are just the tip of the iceberg. Beneath the surface lies a more stealthy tracker: fingerprinting. And here's where it gets even more interesting—–using VPNs won't necessarily protect you from this silent tracking method.
Unlike cookies that announce their presence with pop-ups and permission requests, fingerprinting works in the shadows. It quietly examines your device and browser's unique characteristics, pinpointing your online identity without needing to store anything on your device. As more people adopt tools to block cookies, fingerprinting has become the new way for websites to track your every move, silently.
Imagine every research you make on sensitive topics, health enquiries, financial explorations, and private communications, silently logged and analyzed, forming an invisible profile of you. In this article, we'll shed light on fingerprinting: what it is, how it works, and how to defend against it.
The Basics of Fingerprinting
At its core, fingerprinting is a method used by websites to recognize and track users based on the unique attributes of their devices and browsers. Instead of relying on stored data like cookies, fingerprinting observes and gathers data from the user's device in real-time.
Imagine walking into a room where someone notes down your height, hair color, facial features, and even the way you talk. That's how fingerprinting works. It observes the fonts you've installed, the plugins you use, your screen resolution, the browser you prefer, and even how your device manages tasks. By piecing these details together, a distinct profile is created, unique to you.
Now, comparing fingerprinting to the more familiar cookie-based tracking:
-
Storage: Cookies work by storing small pieces of data on your device. Every time you visit a site, that cookie is read to remember you. On the other hand, fingerprinting doesn't store anything on your device. It simply observes and takes notes.
-
Consent: You've likely come across those pop-ups asking for permission to store cookies. This is because laws in many regions require websites to obtain user consent. Fingerprinting, being more covert, often happens without any such notice or consent.
-
Evasion: As users have become savvy about cookies, many now use tools or browser settings to block them. Fingerprinting, however, is more challenging to detect and prevent, making it an increasingly favored method for tracking by some websites.
Understanding these basics sets the foundation for our deeper dive into the mechanics of fingerprinting, its use cases, and the tools available for defense.
The Mechanics Behind Fingerprinting
When it comes to fingerprinting, the devil is in the details. The more specifics the process can gather, the more accurate the profile. Let's delve into how this mechanism works.
Data Collection Points
First, fingerprinting is not limited to a single piece of information; it gathers various data points to make tracking more effective. Here are some:
-
Device Type: Whether you're on a smartphone, tablet, or computer.
-
Screen Resolution: The exact pixel dimensions of your display are recorded.
-
Browser Type and Version: The browser you're using, down to the version number, can be a crucial identifier.
-
Installed Plugins: If you've got plugins like Flash or an ad blocker.
-
Font List: The fonts installed on your system are a surprisingly specific way to recognize you.
-
Operating System: Whether it's Windows, macOS, Linux, or something else, your OS is a key identifier.
Assembling the Fingerprint
Once these data points are collected, the next step is to assemble them into a fingerprint. The combination of these attributes, when placed correctly, forms a unique profile that can identify you. Here's how it works:
-
Aggregation: First, each of the gathered attributes is logged. This data is compiled into a single record.
-
Hashing: This aggregated data is then run through a hashing algorithm. The result is a string of numbers and letters that serves as your unique identifier.
-
Cross-Reference: Websites can compare this unique hash against a database of previously recorded fingerprints. If there's a match, you're identified; if not, a new fingerprint is stored.
-
Updates: If any attribute changes (like if you update your browser), the fingerprint might change slightly. However, some elements usually remain constant, maintaining a certain level of identification accuracy.
The end product is a unique or near-unique profile that allows websites to recognize you every time you visit, even if you've taken steps to delete cookies or use a VPN.
Real-Life Implications
Fingerprinting may seem like a clever piece of tech, but its ramifications stretch far beyond just better-targeted ads. It raises critical questions about privacy and user consent that you should be aware of.
User Privacy Concerns
Fingerprinting might not seem overtly invasive because it's invisible. However, by quietly collecting various data points, it paints a comprehensive picture of your habits, preferences, and, most worryingly, your confidential activities.
-
Health Searches: Let's say you're researching sensitive medical conditions. Fingerprinting could record this activity, potentially affecting how insurance companies view your profile.
-
Financial Scrutiny: When you're checking investment options or considering a loan, this information could be captured, potentially affecting credit decisions made about you.
-
Workplace Risks: If you're doing market research for a confidential project, fingerprinting can risk that confidentiality, possibly exposing sensitive information to competitors.
Defending Against Fingerprinting
While fingerprinting is a sophisticated technique, it's not entirely unbeatable. There are ways to defend against it, although they come with trade-offs. Here are some strategies:
Browser Configuration
-
Use a Privacy-Focused Browser: Browsers like Tor and Brave are engineered to minimize the extent of data collection and fingerprinting. Tor, for example, routes your traffic through multiple nodes, making it challenging for websites to track you. Brave blocks third-party cookies and trackers by default.
-
Disable JavaScript: Many fingerprinting techniques rely on JavaScript. Disabling it can mitigate tracking, though it may compromise some site functionality.
-
Incognito/Private Mode: While not foolproof, incognito or private browsing modes can offer a degree of protection. They prevent local storage of data, including cookies, although fingerprinting can still occur.
Extensions and Tools
-
Random User-Agent Spoofer: This extension alters your browser’s user-agent ( a string that identifies your browser) to a randomly selected one after a set interval, making fingerprinting more difficult. Get it on the Chrome Web Store. You can also do a quick search for similar extensions and tools like this one on your browser's extension store or search engine.
-
Privacy Badger: While not specifically designed for fingerprinting, this extension blocks spying ads and invisible trackers, which might be used for fingerprinting. Get it on the Chrome Web Store.
-
NoScript: Allows JavaScript, Flash, and other executable content only from trusted domains, adding a layer of protection against fingerprinting, since many fingerprinting techniques rely on JavaScript. Get it on the Chrome Web Store.
-
Multi-Hop VPNs: While VPNs can't entirely prevent fingerprinting, using a multi-hop VPN can make your traffic harder to analyze.
OS-Level Countermeasures
-
Virtual Machines: Running a browser in a virtual machine can help mask your actual system attributes. Some examples of virtual machines include VirtualBox and VMware.
-
OS Tweaking: Some OS settings can be configured to minimize the data exposed to fingerprinting scripts. Guides for doing this are available for various operating systems.
Legislative Measures
-
General Data Protection Regulation (GDPR): Although GDPR doesn't explicitly address fingerprinting, it does emphasize the importance of user consent for data collection. The regulation can be applied to fingerprinting if a case can be made that it constitutes "personal data," which is subject to GDPR protection. However, because fingerprinting often flies under the radar, enforcement varies and many websites evade scrutiny.
-
California Consumer Privacy Act (CCPA): Unlike GDPR, CCPA allows consumers to opt out of the "sale" of their personal information. This can include fingerprinting data, depending on how broadly "sale" is interpreted. The catch is that the CCPA doesn't clearly define what constitutes fingerprinting, leaving room for legal loopholes.
Adding another layer, both laws offer "right to know" and "right to delete" provisions. This means that theoretically, users can request to know what data has been collected via fingerprinting and ask for its deletion. However, because fingerprinting is designed to operate covertly, discovering its use and applying these rights can be challenging.
While these legislative measures provide some avenues for defense, they're not foolproof solutions. The main challenge remains: fingerprinting often goes undetected, making it hard for these laws to be effectively enforced.
Conclusion
Fingerprinting is a growing concern in online privacy. Although there are tools and laws aiming to limit its impact, they're not perfect. The challenge with fingerprinting lies in its ability to operate discreetly, making it hard for both tech solutions and legal measures to keep up effectively.
GDPR and CCPA offer some protection but are limited by inconsistent enforcement and loopholes. Users need to be proactive in using available tools and keeping themselves updated on privacy matters.
As tracking technology advances, methods for evading detection will likely improve as well. Keep yourself educated on your privacy options and stay informed about the latest developments in this space by following me on NewDev, X/twitter, and LinkedIn.
If you found this article useful, then you'll like my JavaScript book, Simplified JavaScript for VIPs. It's one of the simplest JavaScript books you'll find on the internet. Get it here.
Use NextJob to land your next role, manage your job search, generate tailored resumes and cover letters that match each role you apply to. Sign up.
Read my new article on how to land your dream job here: How to Land Your Dream Job: A Step-by-Step Guide for Career Changers.
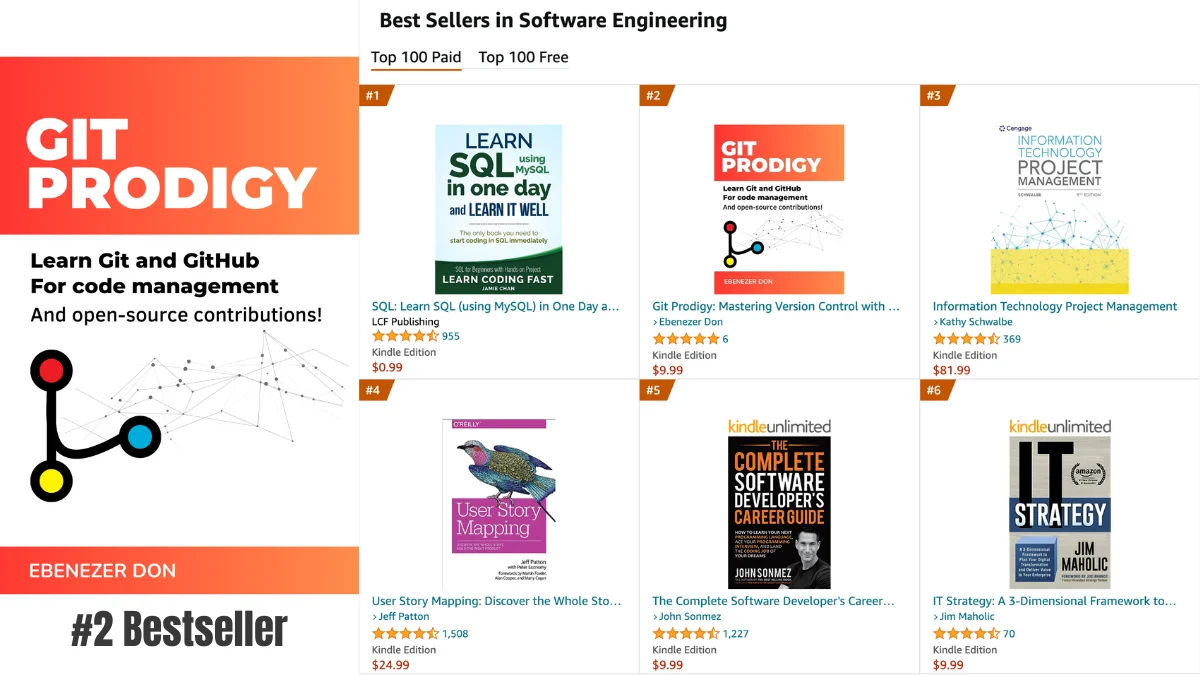
If your goal is to become a top-tier developer, mastering Git is non-negotiable. You need to learn beyond pulling and pushing to create quality software. Get my book, Git Prodigy. Master Version Control and open-source collaboration.